Sei Research Initiative
Part 2: Finality Is a Lie (That We All Agree On)
Mar 19, 2026

By Alejandro Ranchal-Pedrosa
Note: This is Part 2 of Finality Is a Lie (That We All Agree On). For Part 1, see here.
Making finality measurable: Economic security and the Nakamoto Coefficient
The definition above is qualitative. Two quantities make it measurable: the cost to corrupt the quorum and the number of independent entities that must collude. We formalize both.
Economic Security. Let S denote the total stake (or hashrate) securing a protocol, and let f/n denote the maximum fraction of Byzantine participants the protocol tolerates. The economic security E of finality is the minimum cost an adversary must pay to cause a safety violation:
E = α · S
where α is the critical threshold: α = 1/3 for classical BFT (n = 3f+1), α = 1/5 for fast-path BFT (n = 5f+1), or α = 1/2 for Nakamoto consensus. The key question is what "cost" means in practice. In PoW, Budish [28] shows the cost is a flow cost: the adversary must sustain expenditure proportional to block rewards R multiplied by attack duration T, giving E_PoW ≈ R · T. Once the attack ends, the adversary keeps their hardware, so the net cost approaches zero minus opportunity costs. In PoS with slashing, Budish, Lewis-Pye, and Roughgarden [29] show the cost transforms into a stock cost: the adversary's entire corrupted stake α · S is confiscated, giving E_PoS = α · S. This is a one-shot, irrecoverable loss.
For the same S, moving from n = 3f+1 to n = 5f+1 reduces economic security from S/3 to S/5, a reduction of exactly 1 − 3/5 = 40%. Budish, Lewis-Pye, and Roughgarden formalize the desirable property as EAAC (Expensive to Attack in the Absence of Collapse): attacks on consistency must be expensive without requiring collateral damage to honest participants (such as a token price crash). They prove EAAC is achievable in the synchronous PoS model with slashing, but impossible in partial synchrony for adversaries ≥ 1/3 of stake, and impossible in PoW for adversaries ≥ 1/2 of hashrate [29].
Ranchal-Pedrosa and Gramoli show that economic security can be recovered through a combination of accountability, slashing, and recovery [34, 36, 41]. This transforms Budish et al.'s impossibility into a quantitative design constraint: rather than requiring that attacks are always expensive (EAAC), it suffices that the expected punishment from slashed deposits exceeds the expected gain from successful attacks, a property achievable even in partial synchrony with appropriate parameterization.
The Nakamoto Coefficient. Let entities have controlling shares s_1 ≥ s_2 ≥ … ≥ s_n over a subsystem (mining pools, staking operators, client implementations, etc.). The Nakamoto Coefficient [33] for threshold τ is:
NC(τ) = min{ k : Σ(i=1 to k) s_i > τ }
where τ = 1/2 for PoW (51% attack) or τ = 1/3 for BFT safety. The system-wide coefficient is NC_sys = min(NC_mining, NC_staking, NC_clients, NC_exchanges, …), since an attacker need only compromise the weakest subsystem. Current approximate values: Bitcoin NC ≈ 2–3 (at τ = 0.51 hashrate), Ethereum NC ≈ 5 (at τ = 0.33 stake).
The practical cost to revert finality is then bounded by the product of economic security and the coordination difficulty implied by the Nakamoto coefficient. An adversary needs to corrupt NC independent entities whose aggregate stake exceeds α · S. If each entity's cooperation must be individually bribed or compromised, the true cost includes not just the slashable stake but also the coordination cost across NC independent actors, each with distinct incentives, jurisdictions, and risk profiles.
Both quantities interact with network assumptions (as discussed in the Generations of Consensus [25]) to shape what finality actually guarantees. A chain with E = $10B and NC = 3 has a very different finality profile than one with E = $10B and NC = 50: same total cost, but the latter requires coordinating fifty independent conspirators (assume sybil resistance).
What are you trusting, and how much?
A blockchain commitment is only as credible as the full stack underneath it. This section describes the layers of that stack, then maps different systems, assumptions and latencies onto the resulting trust spectrum for finality.
The stack
Social layer. Who decides what software is "the real chain," which clients are valid, how upgrades happen, and what "counts" as a violation worth coordinating around. Ethereum's own documentation explicitly acknowledges that PoS systems can fall back to social coordination in extreme events, and that the community can choose to ignore an attacker's fork and continue building a minority chain [5].
Protocol layer. Protocols are proven to guarantee safety and liveness under assumptions. The key distinction for finality is the separation between safety assumptions and liveness assumptions. The FLP impossibility result [7] shows that deterministic consensus is impossible without timing assumptions. Protocols escape FLP with either a timing assumption (synchrony, partial synchrony, granular synchrony, etc.) or through randomness (which ensures deterministic safety, but not liveness).
In practice, every blockchain protocol in production embeds synchrony assumptions somewhere, even if they claim otherwise. Sei's consensus uses timeouts, making it weakly synchronous for liveness even if safety holds under asynchrony [9]. Ethereum's Casper FFG provides asynchronous safety, but liveness requires >2/3 of validators to be online and reachable, and the inactivity leak is itself synchrony-dependent [10]. Algorand assumes loosely synchronized clocks for liveness recovery [26]. Even Bitcoin's probabilistic finality depends on an implicit synchrony assumption: the honest majority must hear about new blocks faster than the adversary can extend a competing chain [27].
Cryptoeconomic layer. The economic security metrics defined in Part 1 (E, NC) live here. The key structural distinction is between exogenous and endogenous security.
In PoW, security is exogenous: it derives from physical resources (hardware and energy), and the cost of attack is a flow cost that must be continuously sustained [28]. Miners face no protocol-level punishment; the adversary keeps their hardware after attacking, so the net cost approaches zero minus opportunity costs. Bonneau et al. [37] estimate the cost of a majority attack on Bitcoin as bounded by total mining revenue over the attack duration; Bonneau [38] shows that renting hashpower reduces this further; and later [39] identifies a PoW-specific vulnerability: as an attacker credibly accumulates capacity, existing miners may "race to the door" to sell hardware before it becomes worthless, creating a vicious cycle that lowers takeover cost. This dynamic does not exist in PoS, where stake is destroyed endogenously rather than resold.
In PoS, security is endogenous: staked tokens that can be programmatically destroyed. Without slashing, PoS has the same flow-cost problem as PoW. With slashing, the cost transforms into a stock cost: the attacker risks their entire stake, not just opportunity costs [29]. This is the fundamental economic advantage of PoS finality: penalties break the 1:1 ratio between cost of attack and cost of defense [30]. Lewis-Pye and Roughgarden [27] proved that PoS can produce certificates that PoW fundamentally cannot, enabling the accountability → slashing → EAAC chain described in Part 1.
There are two structurally distinct attacks on reverting PoS finality, whose costs depend on the fault model:
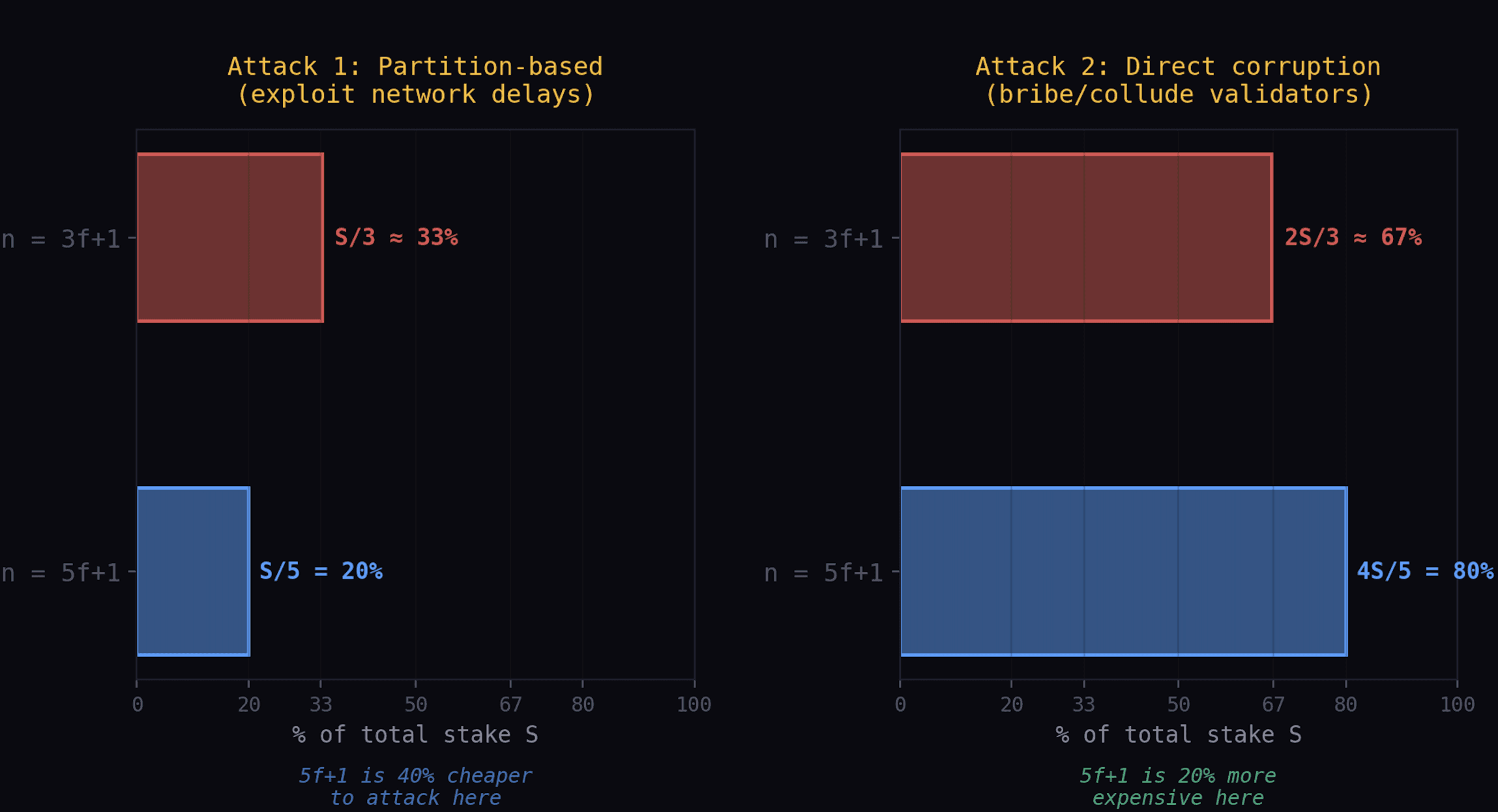
Attack 1 (partition-based): the adversary controls ≥ f+1 stake and exploits network asynchrony to produce conflicting quorum certificates. Cost: S/3 in 3f+1, S/5 in 5f+1.
Attack 2 (direct corruption): the adversary controls a full quorum (≥ n−f stake) and produces conflicting certificates without network manipulation. Cost: 2S/3 in 3f+1, 4S/5 in 5f+1.
Attack 1 requires tight network control; Attack 2 requires only bribery or collusion. Under probabilistic synchrony, waiting exponentially suppresses Attack 1 while Attack 2 remains constant — the full crossover analysis is in the 3f+1 vs 5f+1 section below.
Long-range attacks. Both attacks can target past views if the attacker eclipses nodes running behind, since old replicas may have already liberated their stake. This motivates implicit synchrony assumptions in PoS systems, whereas PoW systems are protected against long-range attacks (though they assume probabilistic synchrony for any notion of finality). Interestingly, any past consensus view where a forking branch was almost decided but failed to be decided is the best candidate for attackers — reducing the economic security against long-range attacks from 66% (resp. 80%) to 33% (resp. 20%) in the n=3f+1 (resp. n=5f+1) model. The economic security can be brought back to their theoretical maxima in these cases via a dedicated round of consensus to agree on decisions (as Filecoin's finality gadget, f3, currently does).
The spectrum
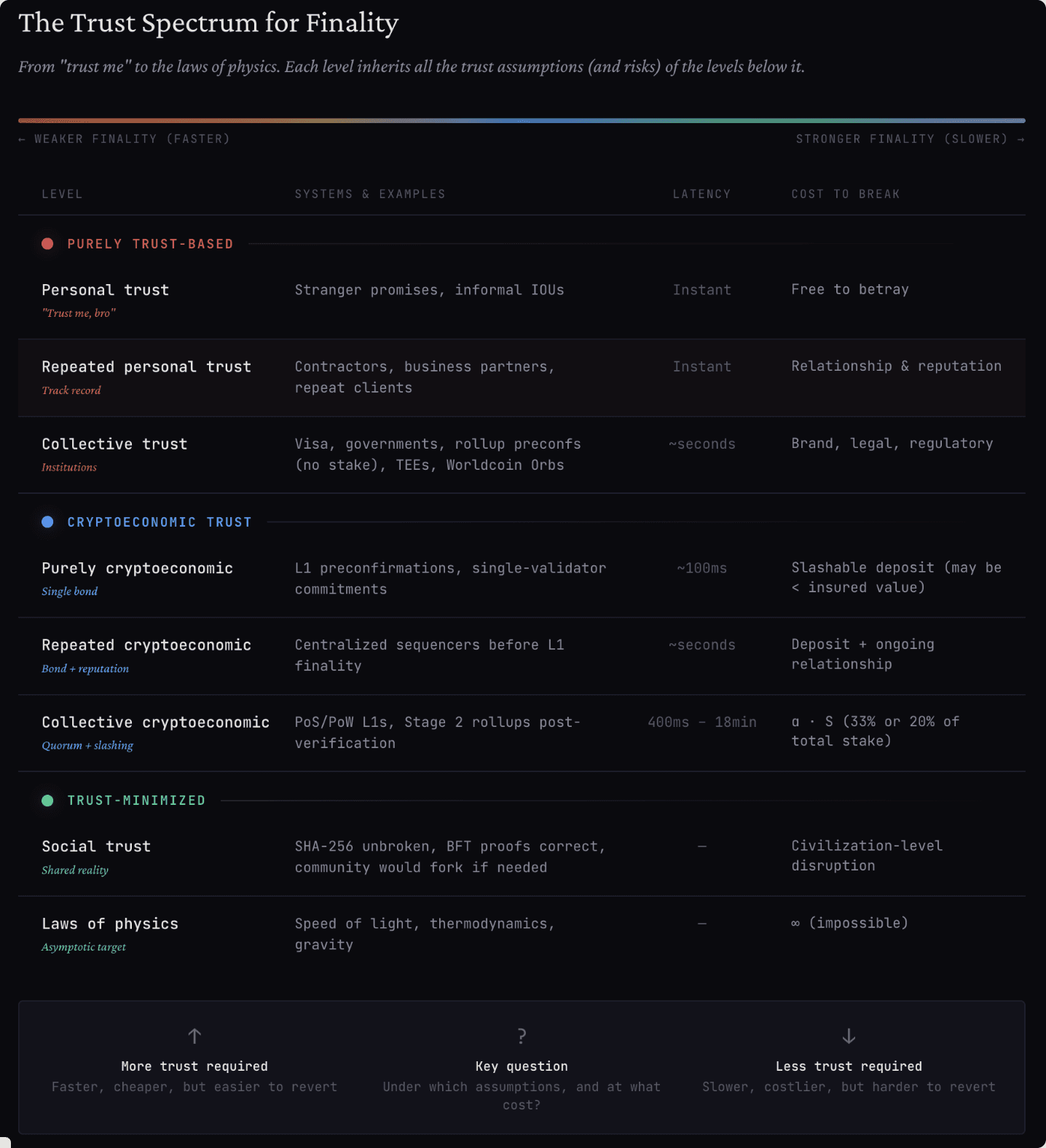
Each of the stack layers above (social, protocol, cryptoeconomic) contributes differently depending on where a system sits on the trust spectrum, and on the user's assumptions and admissible latency. The spectrum ranges from purely trust-based to trust-minimized; with upper levels inheriting all the trust (and risk) from the lower levels, often at faster latencies.
Purely trust-based
Personal trust. The committer says "trust me," you have never met them and do not expect to interact again (e.g. a stranger asking for money and promising to return it).
Repeated personal trust. A personal or professional relationship with the committer creates game-theoretical interest in not breaking the connection (e.g. a contractor asking for more time to perform a task, who has regularly completed tasks before).
Collective trust. The committer is known and respected, or enforced and controlled by a greater committer that is known and respected, or a mix (e.g. Visa, Facebook, Instagram, first-world governments). Rollup preconfs before a commitment is included in L1 and verified (via full-node replication or verifying a proof), unless they are accompanied by some stake (in which case they fall in the repeated cryptoeconomic case). Certain hardware also falls here, as they rely on multiple layers of trust (designer, manufacturer, online list of keys associated with the device, etc.): Trusted-execution environments, biometrics (e.g. Worldcoin's Proof-of-Personhood).
Cryptoeconomic trust
Purely cryptoeconomic. A single cryptoeconomic commitment that can be slashed, e.g. L1 preconfirmations. If the slashed amount is lower than the insured amount, these preconfs can actually be less trustworthy than collective trust (e.g. L1 validator preconf-ing with small stake is less reliable than a centralized sequencer of a long-running rollup).
Repeated cryptoeconomic. Centralized sequencers of rollups before commitment finality and verification. Here, reputation and recurring economic relationships build credibility beyond a single bond.
Collective cryptoeconomic. Decentralized protocols with economic security (Proof-of-Stake/Work). The credibility of finality here depends on the cost to corrupt the quorum, the fault tolerance threshold, decentralization, and whether the stake is exclusive collateral or rehypothecated via restaking. Small PoS chains with concentrated validators sit at the low end; Bitcoin and Ethereum, with billions in security budget and years of undisturbed uptime, sit at the high end. Stage 2 rollups after commitment, verification, and finalization on L1 would also belong here, inheriting the economic security of the underlying L1. The combination of large economic security, decentralized validator sets, and long unbroken track records places systems in this section that have large economic security closest to the trust-minimized end of the spectrum.
Trust-minimized
Social trust. Collective realities that underpin everything else: research results that are not personally formally proven but instead taken as vox populi, common sources of information, widely shared assumptions and economic models. This includes the assumption that SHA-256 is not broken, that the BFT proofs in the papers are correct, that widely used software and hardware is reliable, and that the community would coordinate a social fork if catastrophic failure occurred. Ethereum's documentation explicitly acknowledges this fallback [5]. Recall that Halpern and Moses prove that this is an assumption and impossible to achieve in a distributed system [16].
Laws of physics. Never fully attainable, but aimed for. Speed of light, gravity, thermodynamics. Objective realities that no adversary can alter under the assumptions with which all humans already live (trust in their own senses and experience of the world). The asymptotic target.
Assumptions matter
The finality stack and spectrum above interact in ways that most finality claims gloss over. Worldcoin relies on proof of personhood through biometric hardware (Orbs) designed, manufactured, and attested by a single company. Stage 0 and Stage 1 rollups rely on centralized sequencers before commitments, and even after on security councils of roughly a dozen entities. TEE-based systems rely on Intel or AMD's attestation infrastructure (and even on AWS). CBDCs rely on governments. Each of these sits at a different point on the spectrum above, but their finality claims rarely make this explicit. The availability-finality dilemma [31] formalizes a universal constraint: no blockchain can simultaneously guarantee liveness under dynamic participation and safety under network partitions. Ebb-and-flow protocols [31] resolve this by maintaining two ledgers (a dynamically available one and a finalized prefix), making explicit what most chains leave implicit.
We focus on two main trends that are reshaping the entire web3 ecosystem and whose implications to the economic security for finality of a decentralized L1 is often not well understood: the move to the 5f+1 model and restaking.
The 3f+1 vs 5f+1 trade-off
Classical BFT requires n ≥ 3f + 1 to tolerate f Byzantine faults. That fault model defines the coalition size required to break safety [8]. In a PoS interpretation, finality is backed by at least 33% of total stake.
Some designs buy lower latency by changing this requirement. FaB Paxos achieves two-step Byzantine consensus but requires 5f + 1 replicas [17]. Solana's Alpenglow [18] has become the first major L1 to adopt this model.
In a permissionless PoS interpretation, economic security tracks the fault threshold: in a 3f+1 world, the economic security of finality for partition-based attacks is S/3 where S is total stake; in a 5f+1 world, it drops to S/5, roughly a 40% reduction. The word "finality" is the same; the economic commitment behind it is not.
Accountability with synchrony helps more in 5f+1. The analysis above assumes worst-case partial synchrony. Under probabilistic synchrony (the assumption that the probability of there being a message sent that an observer has not heard of decreases exponentially with time, much like Bitcoin's model), Lewis-Pye and Roughgarden [35] formalize recoverable fault-tolerance: if we accept that a bounded number of consistency violations can occur (each recoverable via rollback and slashing), then fault tolerance can exceed the classical 1/3 bound. A 5/9-bounded adversary (~55% of stake) can cause at most one consistency violation; a 2/3-bounded adversary at most two. Each triggers recovery via accountability proofs, slashing, and rollback [34].
This reframes the trade-off. In the fast path, a committed block carries E_fp of total stake as attestation weight:
E_fp(3f+1) = 2S/3, E_fp(5f+1) = 4S/5
For a block to be reverted, the adversary must produce a conflicting certificate, which requires corrupting validators whose stake exceeds the non-overlapping portion of the two quorums. The standard comparison stops here: partition-based attacks are cheaper in 5f+1, but direct corruption ones are more expensive and, as mentioned above, an explicit decision round can bring focus on to the latter attack.
Waiting eliminates partition-based attacks. The ZLB analysis [34] formalizes this for repeated consensus. Let ρ < 1 be the per-block probability that a partition-based attack succeeds (i.e., that the adversary sustains the required network control). An attack must persist across w consecutive blocks to revert a transaction at blockdepth w, so the probability of a sustained partition-based attack is bounded by ρ^(w+1), which decays exponentially. By contrast, direct corruption does not depend on network conditions — if the adversary controls a full quorum, it can produce conflicting certificates regardless of message delivery.
This creates a crossover. Define the effective economic security of finality at blockdepth w as the minimum cost across both attacks:
E_eff(w) = min( (α_partition · S) / ρ^(w+1), α_direct · S )
where α_partition is the stake fraction for partition-based attacks and α_direct for direct corruption. As w increases, the first term grows without bound while the second stays constant, so E_eff(w) converges to α_direct · S. The crossover blockdepth w* where partition-based cost equals direct corruption cost is:
w* = log(α_partition / α_direct) / log(1/ρ) − 1
Computing concretely for a per-block partition probability of ρ = 0.5:
Model | α_partition | α_direct | w* | E_eff(w > w*) |
|---|---|---|---|---|
3f+1 | 1/3 | 2/3 | 0 | 2S/3 ≈ 0.67S |
5f+1 | 1/5 | 4/5 | 1 | 4S/5 = 0.80S |
For ρ = 0.9 (a more adversarial network):
Model | w* | E_eff(w > w*) |
|---|---|---|
3f+1 | 5.6 | 2S/3 ≈ 0.67S |
5f+1 | 12.6 | 4S/5 = 0.80S |
The 5f+1 model requires more waiting to reach its crossover (because the gap between α_partition and α_direct is larger), but converges to a strictly higher effective security: 0.80S vs 0.67S, a 20% improvement. For any observer willing to wait past w* blocks, the 5f+1 model provides more credible finality than 3f+1 with the same total stake.
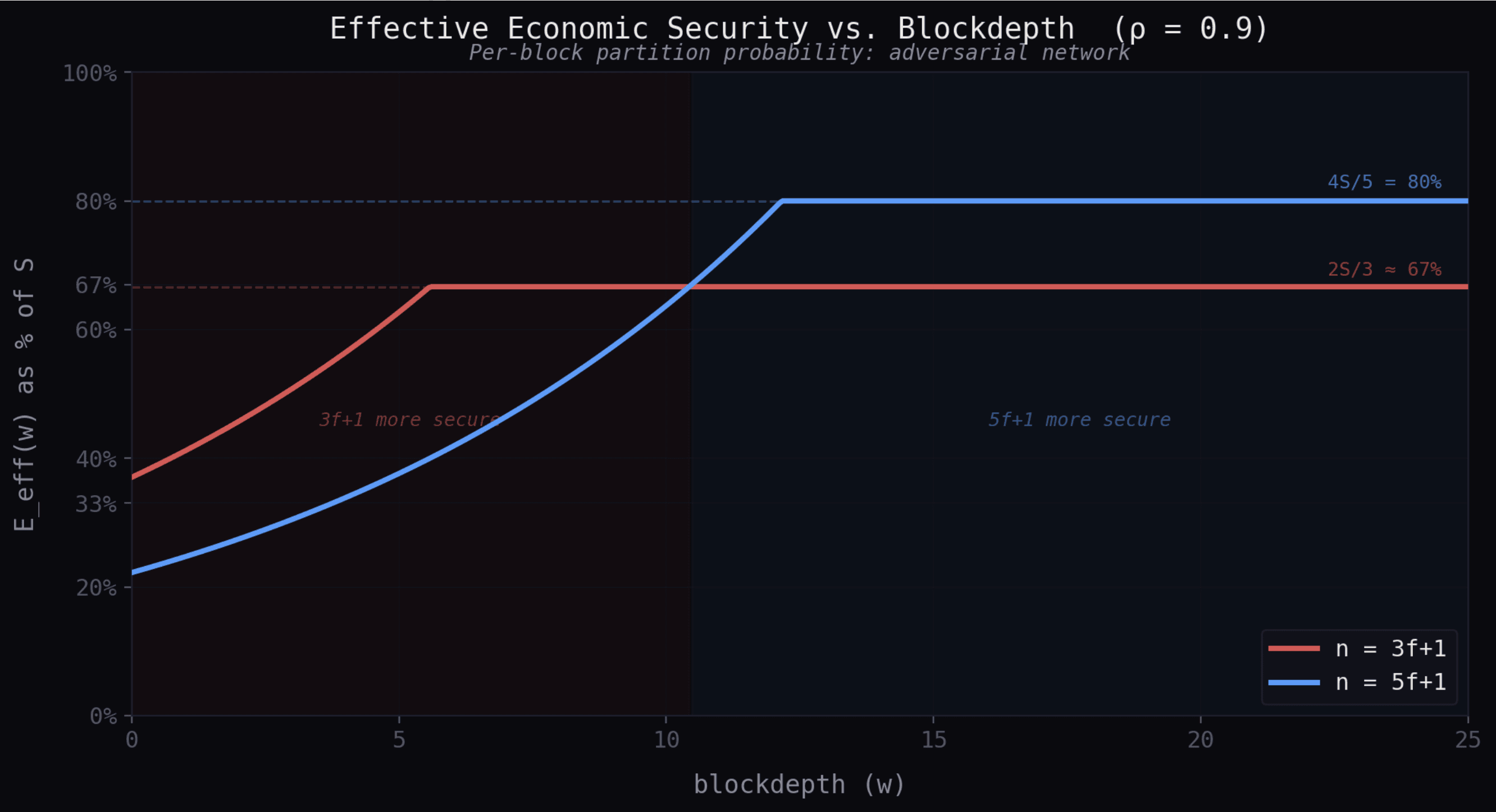
Even in a 3f+1 protocol, an observer who waits zero additional blocks faces an effective security of S/3 (the partition-based threshold). An observer who waits w* blocks faces 2S/3, a doubling. This is the same logic that gives Bitcoin's probabilistic finality its strength: each additional confirmation exponentially suppresses the relevant attack, converging effective security to the cost of direct majority corruption. The difference is that in BFT with accountability, the convergence is formalized through slashing and deposit mechanics rather than through proof-of-work difficulty.
From the ZLB zero-loss payment analysis [34], the deposit flux per attack attempt at blockdepth w is:
ξ = ((1 − ρ^(w+1))b − (a−1)ρ^(w+1)) · G
where b = D/G is the deposit-to-gain ratio and a the number of fork branches. For w > w*, the partition-based term ρ^(w+1) is negligible, so ξ ≈ bG > 0: the system is in permanent surplus, and the deposit fully covers any residual risk. The practical implication is that the 20% fault-tolerance reduction in 5f+1 is not a permanent cost (safety-wise) — it is a transient vulnerability that vanishes with modest waiting (and/or a dedicated decision round), leaving only the permanent advantage of a higher direct corruption barrier.
Restaking changes what collateral secures your "finality"
Restaking systems such as EigenLayer let Ethereum stakers opt into validating new modules by accepting additional slashing conditions on already-staked ETH [19]. As of early 2026, approximately 4.4 million ETH (~13% of all staked ETH, worth ~$15 billion) is restaked through EigenLayer alone, securing dozens of Actively Validated Services (oracles, DA layers, bridges, sequencers) with the same collateral that secures Ethereum's consensus.
This rehypothecation distorts what "economic security" means for downstream finality. Vitalik Buterin's warning about "overloading" Ethereum's consensus [20] is about systemic risk: failures in external obligations can spill back into the base layer. Durvasula and Roughgarden [40] model restaking as a bipartite graph between validators and services and show that robust security requires overcollateralization: for every subset of validators capable of corrupting a set of services, total stake must exceed total attack profit by a factor 1 + γ. If this holds, a shock losing ψ of total stake causes at most (1 + 1/γ)ψ total loss — the cascade is bounded. But if γ ≤ 0 (aggregate attack profit across shared services equals or exceeds the pledged stake), cascading failures can consume the entire restaked pool. The bound is tight. Research on multi-shared-security-provider settings [21] formalizes the complementary fragmentation problem: when an AVS draws security from multiple SSPs, the adversary targets the weakest, and security degrades to the lowest-cost-attack condition.
With 13% of Ethereum's stake already restaked and growing in EigenLayer alone, the economic security of Ethereum is slightly diluted.
Where does Sei sit?
Finality lives at the intersection of fault tolerance thresholds, economic security, the Nakamoto coefficient, and network assumptions. Different chains choose different points in this space. Sei's choice is deliberate.
Sei today uses classical BFT consensus (Twin Turbo Consensus [22], an optimization of Tendermint/CometBFT) with the standard n = 3f+1 partial synchrony model. A block is final when >2/3 of voting power pre-commits, giving deterministic finality under <1/3 Byzantine. Block finality is ~400ms. There is no weaker "preconfirmation" or "soft commit" that users must rely on: the first commitment is already the real one, backed by the same classical BFT guarantee that the field has studied for four decades.
Sei Giga [23] pushes latency further down while keeping the same classical BFT thresholds. It decouples data dissemination, ordering, and execution to remove bottlenecks without weakening the fault tolerance that backs finality [24][25]. Internal devnet benchmarks report 40 nodes across 4 regions, sustained 5 Gigagas, and ~700ms finality [23]. The trajectory is toward even lower latency, but always at the same point on the economic security spectrum: robust unless the world goes sideways.
Conclusion
Sei's trajectory, from Twin Turbo to Sei Giga, is best understood as an attempt to make classical BFT finality operationally valuable: push latency to web-app budgets without redefining what "final" means or weakening the fault tolerance behind it.
Across the industry, the word "finality" is overloaded. Changes like 5f+1-style speed trades can reduce the economic cost to break safety by ~40%. Restaking can rehypothecate the collateral that backs finality across multiple obligations. Rollup sequencer receipts can be marketed as "final" when the underlying settlement has not occurred. Finality never means the same thing for different systems, or for different observers.
Different designs choose different points in this space: probabilistic vs deterministic, trust-based vs cryptoeconomic, high throughput vs security margins, 3f+1 vs 5f+1, isolated staking vs restaked collateral. Understanding these trade-offs is essential for anyone building or using decentralized systems natively.
References
[1] Committee on Payment and Settlement Systems (CPSS). A glossary of terms used in payments and settlement systems. Bank for International Settlements, 2003.
[2] T. C. Schelling. The Strategy of Conflict. Harvard University Press, 1960.
[3] J. Y. Halpern and X. Vilaça. Rational consensus. In Proceedings of the 2016 ACM Symposium on Principles of Distributed Computing (PODC), pages 137–146, 2016.
[4] J. R. Douceur. The Sybil Attack. In Proceedings of the 1st International Workshop on Peer-to-Peer Systems (IPTPS), pages 251–260, 2002.
[5] Ethereum Foundation. Proof-of-Stake FAQ: What happens if the chain finalizes different things? ethereum.org, 2024.
[6] V. Buterin. Long range attacks: The serious problem with adaptive proof of work. Blog post, 2014.
[7] M. J. Fischer, N. A. Lynch, and M. S. Paterson. Impossibility of distributed consensus with one faulty process. Journal of the ACM, 32(2):374–382, 1985.
[8] C. Dwork, N. Lynch, and L. Stockmeyer. Consensus in the presence of partial synchrony. Journal of the ACM, 35(2):288–323, 1988.
[9] J. Kwon. Tendermint: Consensus without mining. Whitepaper, 2014.
[10] V. Buterin and V. Griffith. Casper the friendly finality gadget. arXiv preprint arXiv:1710.09437, 2017.
[11] G. Aggarwal, F. Schär, and G. Fanti. An empirical analysis of stake concentration in Proof-of-Stake blockchains. In 2021 IEEE Symposium on Security and Privacy (SP), pages 1475–1491, 2021.
[12] L2BEAT. Rollup Stages Framework. https://l2beat.com/scaling/summary, 2025.
[13] Etherscan. Ethereum Blocks: Finality Status. https://etherscan.io, 2025.
[14] Trail of Bits. The Engineer's Guide to Blockchain Finality. The Trail of Bits Blog, August 23, 2023.
[15] I. Abraham, V. Buterin, and L. Zanolini. Finality Is in the Eye of the Beholder. Decentralized Thoughts, November 23, 2025.
[16] J. Y. Halpern and Y. Moses. Knowledge and common knowledge in a distributed environment. Journal of the ACM, 37(3):549–587, 1990.
[17] J.-P. Martin and L. Alvisi. Fast Byzantine consensus. IEEE Transactions on Dependable and Secure Computing, 3(3):202–215, 2006.
[18] Q. Kniep, K. Sliwinski, and R. Wattenhofer. Solana Alpenglow consensus. Anza whitepaper, 2025.
[19] EigenLayer. EigenLayer: The restaking collective. Whitepaper, 2023.
[20] V. Buterin. Don't overload Ethereum's consensus. Blog post, 2023.
[21] A. Ranchal-Pedrosa et al. Security analysis of multi-shared-security-provider settings. Working paper, 2025.
[22] Sei. How Sei became the fastest blockchain: Twin Turbo Consensus. https://blog.sei.io/twin-turbo-consensus/, March 2024.
[23] Sei Research Initiative. Sei Giga: Achieving 5 Gigagas with Autobahn Consensus. https://seiresearch.io/articles/sei-giga-achieving-5-gigagas-with-autobahn-consensus, Feb 2025.
[24] N. Giridharan, F. Suri-Payer, I. Abraham, L. Alvisi, and N. Crooks. Autobahn: Seamless high speed BFT. In Proceedings of the ACM SIGOPS 30th Symposium on Operating Systems Principles (SOSP '24), pages 1–23, 2024.
[25] A. Ranchal-Pedrosa. The Generations of Consensus: From Safety-first to Instant Finality. Sei Research Initiative, Dec 2025.
[26] Y. Gilad, R. Hemo, S. Micali, G. Vlachos, and N. Zeldovich. Algorand: Scaling Byzantine Agreements for Cryptocurrencies. In SOSP 2017, pages 533–550, 2017.
[27] A. Lewis-Pye and T. Roughgarden. How Does Blockchain Security Dictate Blockchain Implementation? In ACM CCS 2021, pages 1006–1019; arXiv:2109.04848, 2021.
[28] E. Budish. Trust at Scale: The Economic Limits of Cryptocurrencies and Blockchains. Quarterly Journal of Economics, 140(1):1–62, 2025.
[29] E. Budish, A. Lewis-Pye, and T. Roughgarden. The Economic Limits of Permissionless Consensus. In ACM EC 2024, pages 704–731, 2024.
[30] V. Buterin. A Proof of Stake Design Philosophy. Blog post, 2016.
[31] J. Neu, E. N. Tas, and D. Tse. Ebb-and-Flow Protocols: A Resolution of the Availability-Finality Dilemma. In IEEE S&P 2021, pages 446–465; arXiv:2009.04987.
[33] B. S. Srinivasan and L. Lee. Quantifying Decentralization. news.earn.com, 2017.
[34] A. Ranchal-Pedrosa and V. Gramoli. ZLB: A Blockchain to Tolerate Colluding Majorities. In IEEE DSN 2024, pages 209–222, 2024. (Best Paper Award)
[35] A. Lewis-Pye and T. Roughgarden. Beyond Optimal Fault-Tolerance. In AFT 2025, LIPIcs Vol. 354, pages 15:1–15:23, 2025.
[36] A. Ranchal-Pedrosa and V. Gramoli. TRAP: The Bait of Rational Players to Solve Byzantine Consensus. In ACM AsiaCCS 2022, pages 530–542, 2022.
[37] J. Bonneau, A. Miller, J. Clark, A. Narayanan, J. A. Kroll, and E. W. Felten. SoK: Research Perspectives and Challenges for Bitcoin and Cryptocurrencies. In IEEE S&P 2015, pages 104–121, 2015.
[38] J. Bonneau. Why Buy When You Can Rent? Bribery Attacks on Bitcoin-Style Consensus. In FC 2016 Workshops, LNCS 9604, pages 19–26, 2016.
[39] J. Bonneau. Hostile Blockchain Takeovers (Short Paper). In FC 2018 Workshops (BITCOIN), LNCS 10958, pages 92–100, 2018.
[40] N. Durvasula and T. Roughgarden. Robust Restaking Networks. In ITCS 2025, LIPIcs Vol. 325, pages 48:1–48:21, 2025.
[41] A. Ranchal-Pedrosa. Blockchain Technologies to Tolerate Colluding Majorities. PhD thesis, University of Sydney, 2024.